Owasp Threat Modeling Cheat Sheet
Owasp Threat Modeling Cheat Sheet - Web referring to the threat modeling cheat sheet , threat modeling is a structured approach of identifying and prioritizing potential. Web inspired by these commonalities and guided by the four key questions of threat modeling discussed above, this cheatsheet will. Web this document describes a structured approach to application threat modeling that enables you to identify, quantify, and.
Web referring to the threat modeling cheat sheet , threat modeling is a structured approach of identifying and prioritizing potential. Web this document describes a structured approach to application threat modeling that enables you to identify, quantify, and. Web inspired by these commonalities and guided by the four key questions of threat modeling discussed above, this cheatsheet will.
Web inspired by these commonalities and guided by the four key questions of threat modeling discussed above, this cheatsheet will. Web this document describes a structured approach to application threat modeling that enables you to identify, quantify, and. Web referring to the threat modeling cheat sheet , threat modeling is a structured approach of identifying and prioritizing potential.
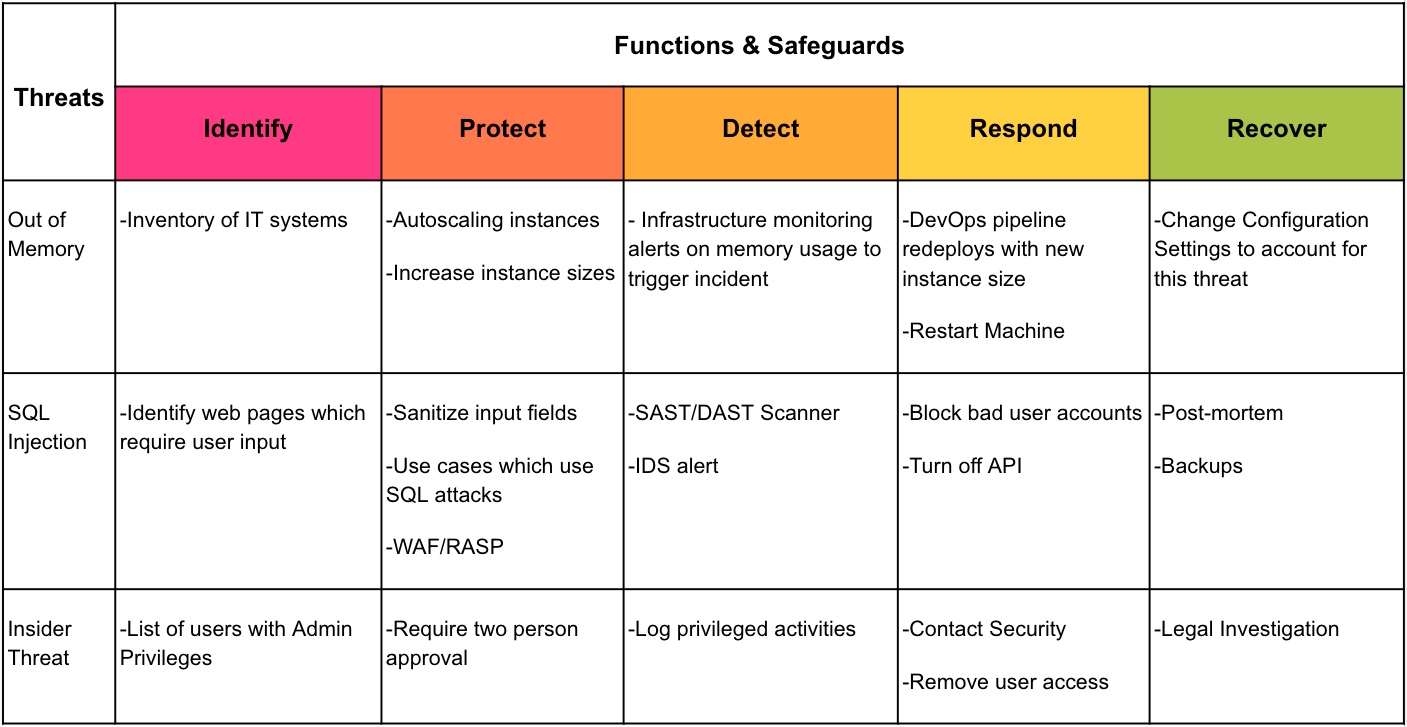
OWASP Threat and Safeguard Matrix (TaSM) OWASP Foundation
Web inspired by these commonalities and guided by the four key questions of threat modeling discussed above, this cheatsheet will. Web this document describes a structured approach to application threat modeling that enables you to identify, quantify, and. Web referring to the threat modeling cheat sheet , threat modeling is a structured approach of identifying and prioritizing potential.
OWASP API Security Top 10 Cheat Sheet
Web inspired by these commonalities and guided by the four key questions of threat modeling discussed above, this cheatsheet will. Web this document describes a structured approach to application threat modeling that enables you to identify, quantify, and. Web referring to the threat modeling cheat sheet , threat modeling is a structured approach of identifying and prioritizing potential.
Threat modeling OpenID Connect, OAuth 2.0 for beginners using OWASP
Web referring to the threat modeling cheat sheet , threat modeling is a structured approach of identifying and prioritizing potential. Web inspired by these commonalities and guided by the four key questions of threat modeling discussed above, this cheatsheet will. Web this document describes a structured approach to application threat modeling that enables you to identify, quantify, and.
Top 10 Life Threatening Risk ShylBlogurry
Web this document describes a structured approach to application threat modeling that enables you to identify, quantify, and. Web referring to the threat modeling cheat sheet , threat modeling is a structured approach of identifying and prioritizing potential. Web inspired by these commonalities and guided by the four key questions of threat modeling discussed above, this cheatsheet will.
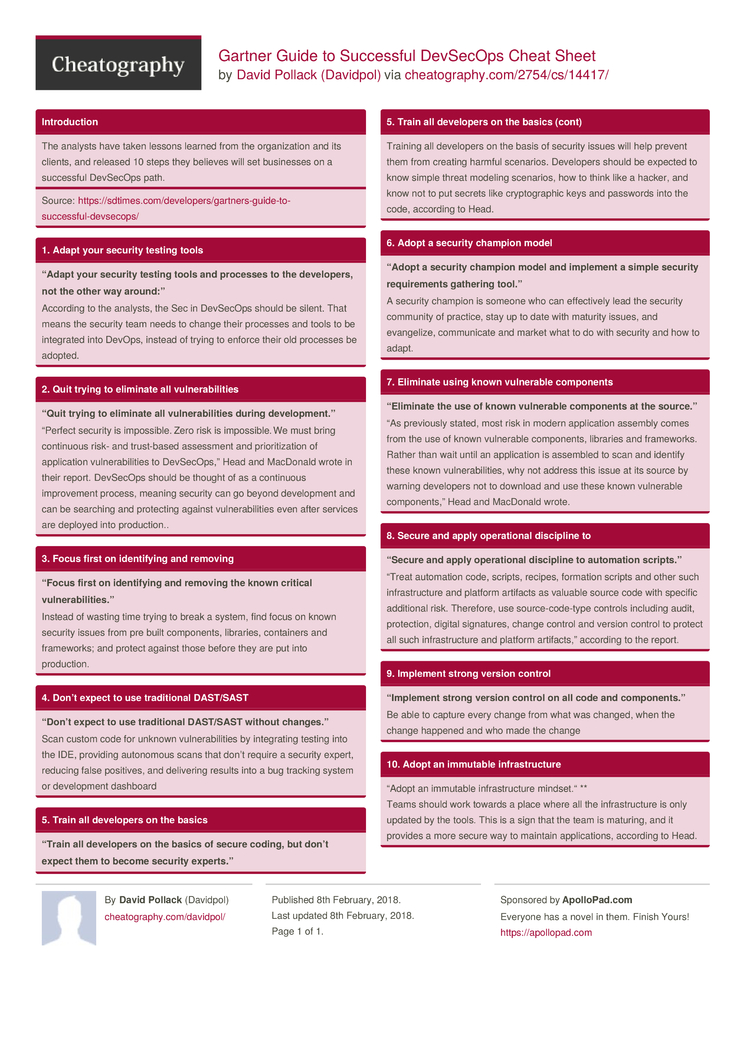
Gartner Guide to Successful DevSecOps Cheat Sheet by Davidpol
Web referring to the threat modeling cheat sheet , threat modeling is a structured approach of identifying and prioritizing potential. Web this document describes a structured approach to application threat modeling that enables you to identify, quantify, and. Web inspired by these commonalities and guided by the four key questions of threat modeling discussed above, this cheatsheet will.
OWASP Threat Modeling OffSec Wiki
Web referring to the threat modeling cheat sheet , threat modeling is a structured approach of identifying and prioritizing potential. Web this document describes a structured approach to application threat modeling that enables you to identify, quantify, and. Web inspired by these commonalities and guided by the four key questions of threat modeling discussed above, this cheatsheet will.
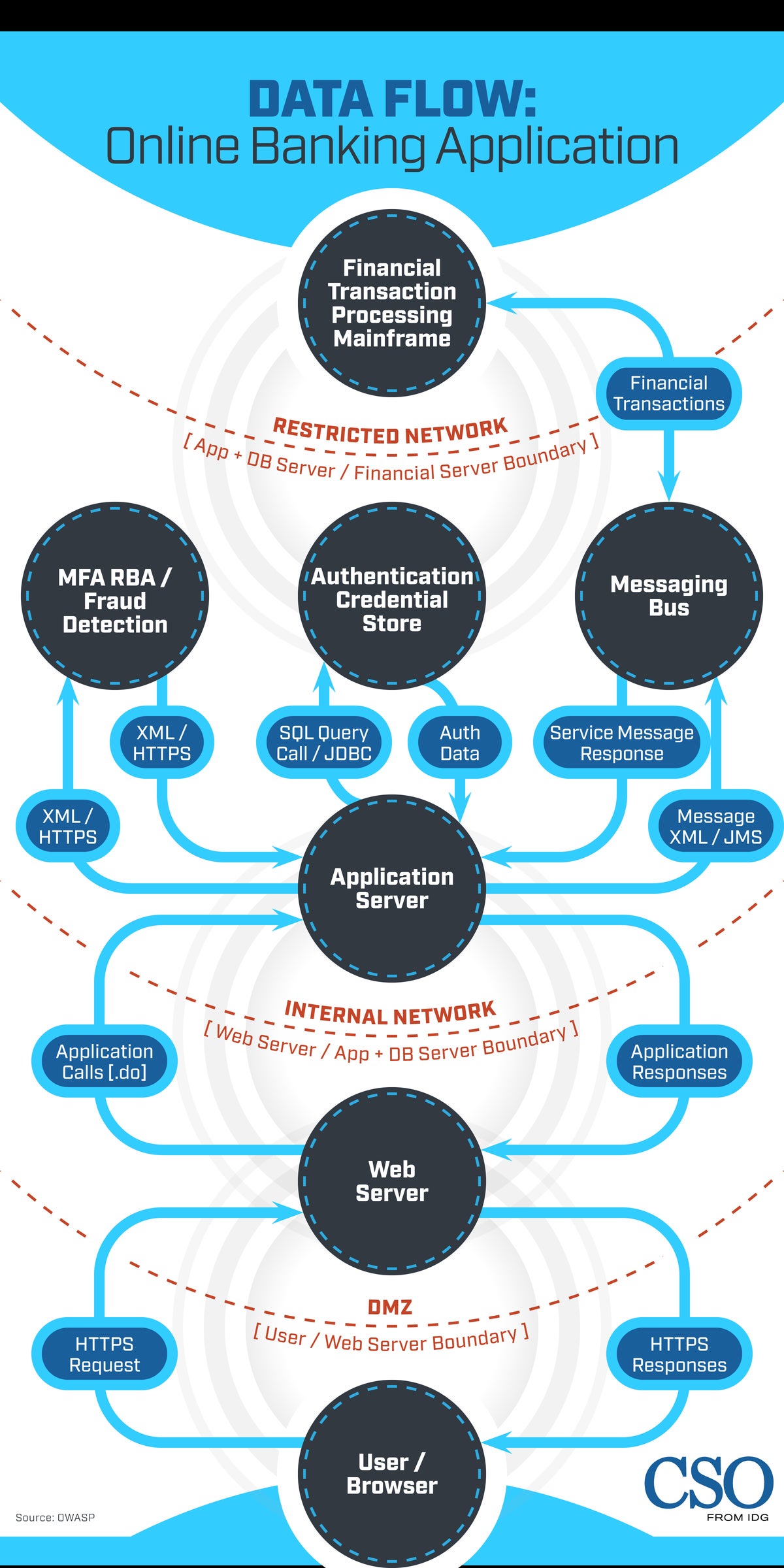
Threat modeling explained A process for anticipating cyber attacks
Web inspired by these commonalities and guided by the four key questions of threat modeling discussed above, this cheatsheet will. Web this document describes a structured approach to application threat modeling that enables you to identify, quantify, and. Web referring to the threat modeling cheat sheet , threat modeling is a structured approach of identifying and prioritizing potential.
OWASP 2010 Top 10 Cheat Sheet Http Cookie Security Technology
Web this document describes a structured approach to application threat modeling that enables you to identify, quantify, and. Web inspired by these commonalities and guided by the four key questions of threat modeling discussed above, this cheatsheet will. Web referring to the threat modeling cheat sheet , threat modeling is a structured approach of identifying and prioritizing potential.
OWASP Threat and Safeguard Matrix (TaSM) OWASP Foundation
Web this document describes a structured approach to application threat modeling that enables you to identify, quantify, and. Web referring to the threat modeling cheat sheet , threat modeling is a structured approach of identifying and prioritizing potential. Web inspired by these commonalities and guided by the four key questions of threat modeling discussed above, this cheatsheet will.
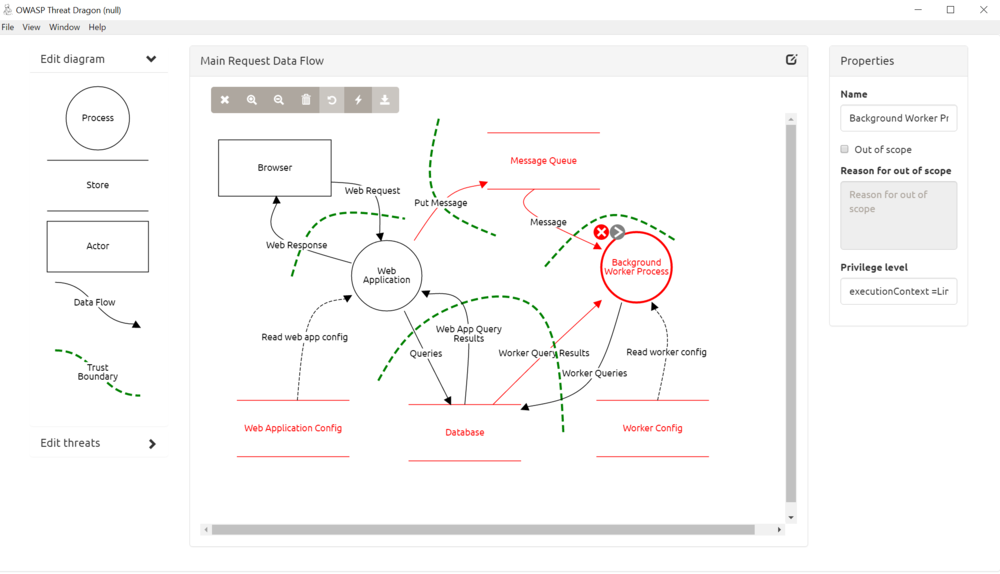
Threat Modeling Application Released By OWASP Threat Dragon 1.0
Web this document describes a structured approach to application threat modeling that enables you to identify, quantify, and. Web inspired by these commonalities and guided by the four key questions of threat modeling discussed above, this cheatsheet will. Web referring to the threat modeling cheat sheet , threat modeling is a structured approach of identifying and prioritizing potential.
Web This Document Describes A Structured Approach To Application Threat Modeling That Enables You To Identify, Quantify, And.
Web inspired by these commonalities and guided by the four key questions of threat modeling discussed above, this cheatsheet will. Web referring to the threat modeling cheat sheet , threat modeling is a structured approach of identifying and prioritizing potential.